Estimated read time: 5 minutes
I often had discussions with customers and colleagues about our security products, which create a private network for safe work. But when I explain what the private network is and how it works, I've got similar questions: how is it possible that data are transferred via the internet; why we are talking about public or private addresses; and what does it mean for us? If you are not a technical expert or tech geek interested in networking, you can feel lost in these discussions.

I will explain how packets and your data flow on the internet and private networks. But also I want to apologise to experts that we will talk about paper boxes and not about bit and bytes.
What Is a Packet?

First of all, I want to describe a thing called a packet and why it is crucial. Internet protocols usually work with some data fragments to effectively ship these data fragments. So if you have a large file, you have to divide it to smaller pieces. It is similar to the real world: if you buy a tanker of oil and transport it to customers, you are loading it to trucks and delivering it in smaller pieces.
The second aspect of internet packets is that data are transferred in a packet without any encryption. Encryption which we know, for example, from secure websites like our internet banking, is managed on higher levels. It means encryption is done between your browser and the internet banking server.
Communication Between two Public Addresses
Let's talk now about communication between two internet addresses or, better, call them public addresses.
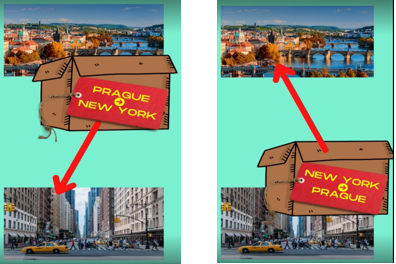
When we want to ship our packet, which I can see like a shipping box, from public address Prague to public address New York, I have to put on my box label describing who the sender and recipient is. It is logical because if we are expecting any response to our request recipient has to know where he can send a reply. So in our example, is the response packet sent from back New York to Prague.
We have to consider that if we send a large amount of data, they are split into packets. The internet is shipping our packets, and it is the responsibility of the sender and recipient to couple packets again to the original large file.
Communication Through a Private Network
Cool, but how it worked when we involved something like a private network which we know from home or office, your office local network or home local WiFi network are good examples of the private network. This small isolated network has connected many devices, which can communicate with each other.
But how can these devices from this private network with private addresses communicate to the outside world?
Again, we can think about this as something we know from the real world. So we can imagine that if we want to send a box from a private area to a standard public address, we have to use some broker. It's like sending a letter from a military base to your family. If you are a soldier and send a letter, the military post collects your letter and sends it via post to your family. If your family sends a reply letter to you, it is addressed to the military base, but with a note, that letter is addressed to you. The military base itself is responsible for routing the letter to you in the private area.

How will it work on our example with boxes?
I am sitting in an office in Prague, and I want to send a packet to New York, but my workplace has no public address. I have only an internal office room number - it is my private address.
I put my data in the packet and stuck label with recipient address New York and my sender address Office Room 1. This packet I send to our office broker. It means to our office Wi-Fi router. Wi-Fi router has public address Prague and router itself put on top on my label new label with sender address Prague and recipient address New York. So the packet is sent via the internet from our router to the destination. When New York wants to send back any packet to me, he uses original labels and only changes the recipient and senders information. So reply packet is travelling back to Prague, to our office router. The office router finally checked the original label with my office room number and sent the packet to my office room. And that's it.
See the flow of our packet on the following picture:

You can practically put many brokers between you and target public addresses. So simply, you are working only with more layers of labels.
Try Shieldoo™️
Cyber security is becoming more and more important, which is why we provide you with essential information in a wide variety of articles on our blog. We also developed a new tool Shieldoo™️ based on Nebula from Slack which can help you to provide secure connection between end-users and servers. You can try your own private network here.
FAQs
What is a packet on internet?
Packet is a basic unit of data that's grouped together and transferred over a computer network. Internet protocols usually work with some data fragments to effectively ship these data fragments. So if you have a large file, you have to divide it to smaller pieces -these are called packets.
What is encryption?
Encryption is the method by which information is converted into secret code that hides the information's true meaning.
What is private network and public network?
A public network is a network to which anyone can connect (e.g. Internet). A private network is any network to which access is restricted (e.g. corporate network or a network in a school).





