Estimated read time: 8 minutes
What Is a DMZ Network?
A DMZ network, short for demilitarized zone, is a perimeter network or a screened subnet work providing an additional layer of security to protect a local area network (LAN) from the vulnerabilities of the public Internet. Outward-facing services and servers such as the domain name system (DNS), email, web servers, and file transfer protocol (FTP) servers are stored in the DMZ to secure the internal network from data breaches and malicious attacks.
In short, a DMZ network is an extra layer of security that enables enterprises to separate private networks from public Internet access and secure critical data. Servers, resources, and services stored in the DMZ have limited access to the LAN, heightening security protocol against uninvited guests.
How Does a DMZ Network Work?
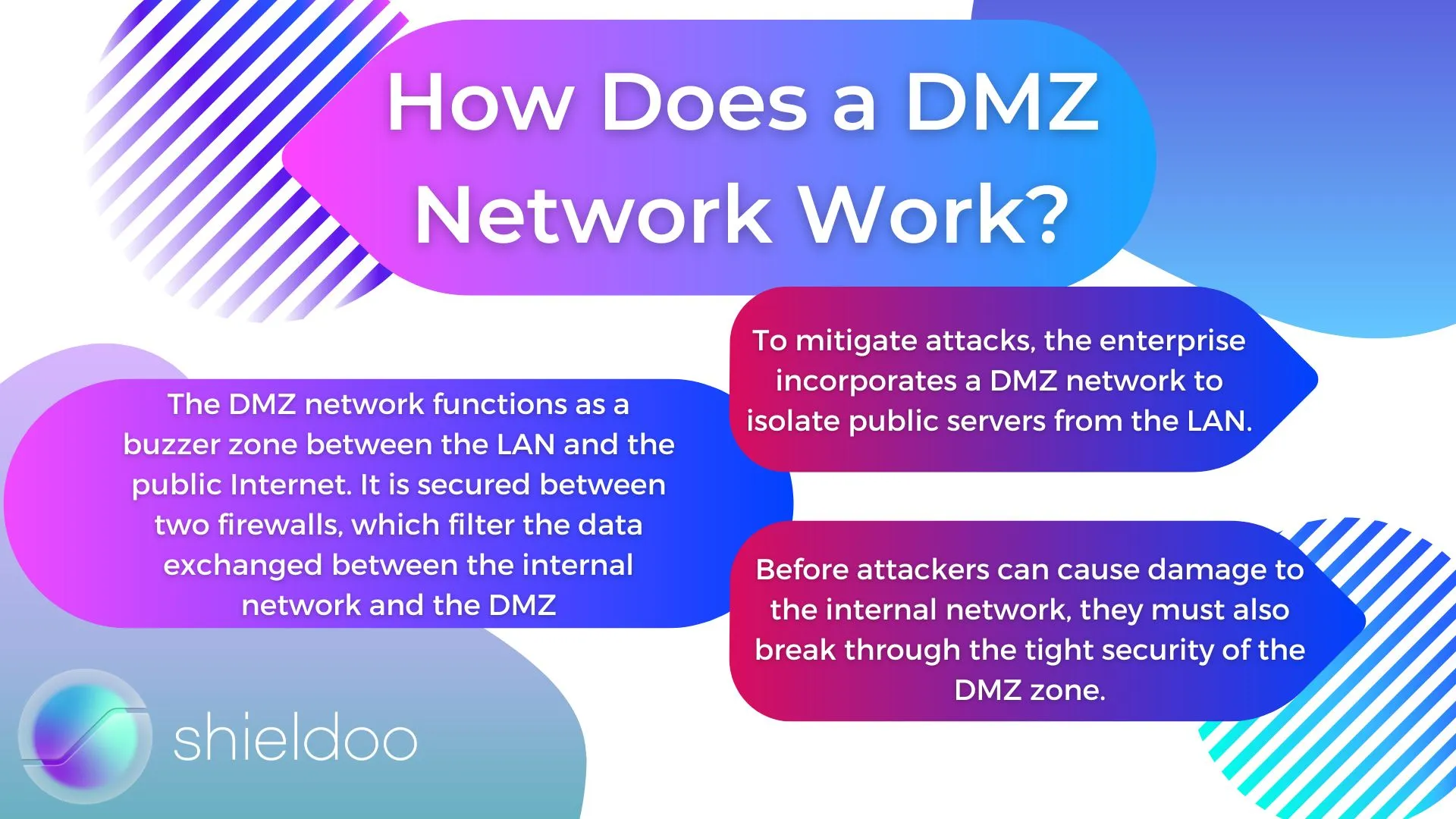
For an enterprise to accommodate the needs of customers, it is essential to deploy a web server on the public Internet. However, doing so comes with the risk of exposing the internal network to security threats. To mitigate attacks, the enterprise incorporates a DMZ network to isolate public servers from the LAN.
The DMZ network functions as a buzzer zone between the LAN and the public Internet. It is secured between two firewalls, which filter the data exchanged between the internal network and the DMZ, and traffic flowing from external networks to the DMZ.
Such a setup enables security measures to screen data packets before they get through the servers in the DMZ. Before attackers can cause damage to the internal network, they must also break through the tight security of the DMZ zone.
What Does a DMZ Network Look Like: Design and Network Architecture
A DMZ can be set up indifferent ways. Firewalls are a staple in constructing a secure DMZ network, with the dual firewall setup as the most commonly used design in DMZ networking.
Single Firewall
A single firewall design needs at least three network interfaces. The DMZ network is secured behind this firewall. An external network sets up the communication path from the public Internet to the firewall. This is made possible by connecting to an internet service provider (ISP). The second network interface connects to the internal network, while the third network interface manages connections to the DMZ network.
Dual Firewall
The dual firewall design is a more secure and scalable network architecture for DMZ. The front-end firewall screens traffic coming into the DMZ network, while the back-end firewall screens traffic moving from the DMZ to the private network.
The Benefits of Adopting DMZ in Network Security
A DMZ network restricts users on external networks from accessing critical data on the private network. Users may access these servers from the public Internet. However, their authorization to interact with such servers is confined within the DMZ network.
The DMZ functions as a buffer area between public users and the private network.
A DMZ network offers an efficient configuration of network security. Due to large influxes of user activity every day, a DMZ network helps enterprises to define user trust on varying levels. Additionally, a DMZ network introduces several security benefits:
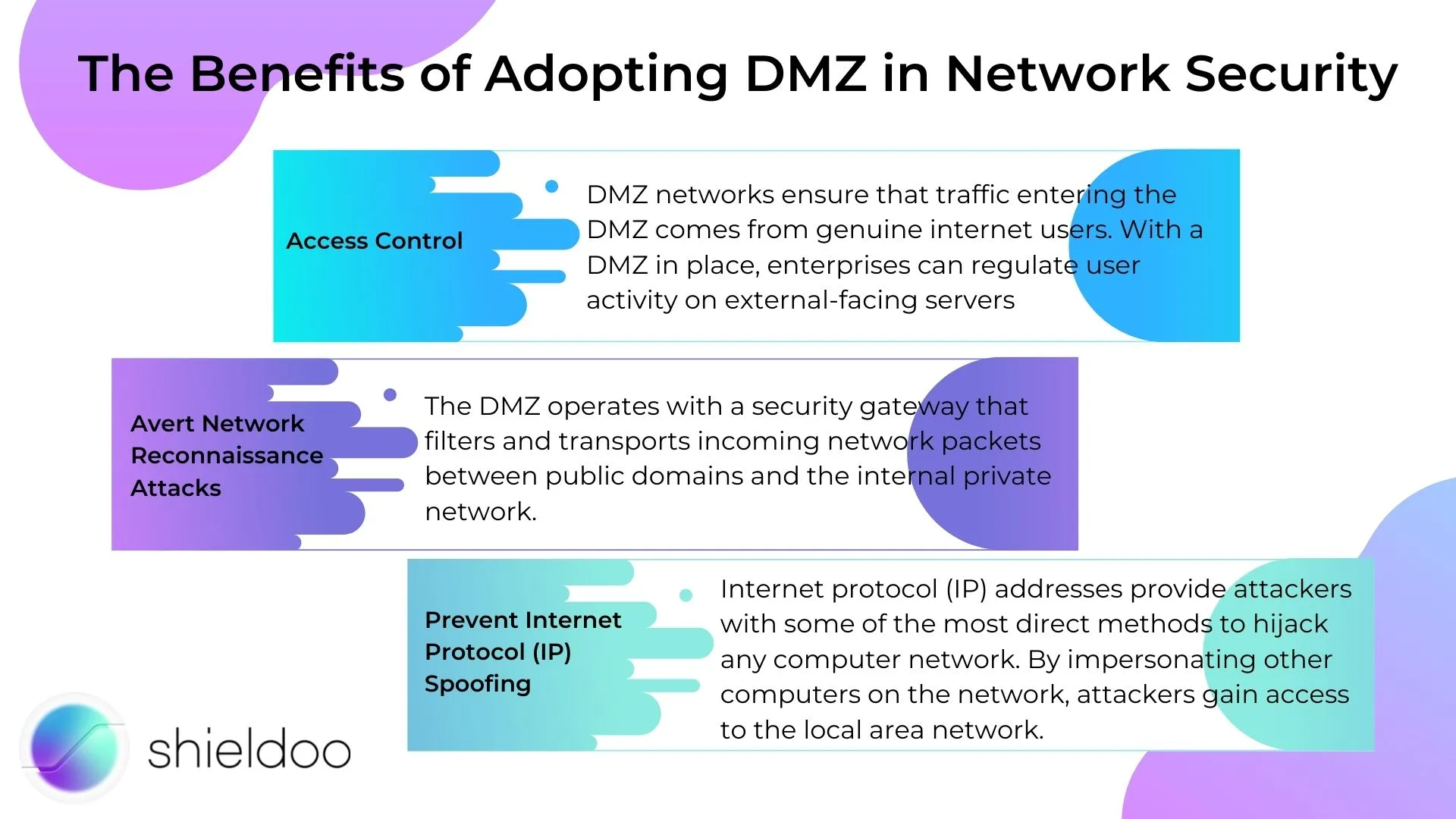
Access Control
DMZ networks ensure that traffic entering the DMZ comes from genuine internet users. With a DMZ in place, enterprises can regulate user activity on external-facing servers. The typical dual firewall design of DMZ networks reinforces the level of security to prevent untrusted networks from infiltrating the local area network. The tighter the security, the more challenging it will be for cybercriminals to hijack past the DMZ and access resources on the local area network.
Enterprises can also introduce a proxy server. A proxy server retrieves and sends user requests, preventing users from getting any closer to the internal network’s perimeter.
Avert Network Reconnaissance Attacks
The DMZ operates with a security gateway that filters and transports incoming network packets between public domains and the internal private network.
With a DMZ acting as a buffer, cyber-attackers cannot launch their reconnaissance attacks. In other words, malicious internet users cannot farm and exploit sensitive client information and company assets.
On the off-chance that the DMZ is compromised, an internal firewall serves as a backup layer of security. It isolates the DMZ from the private network, cutting off any attacker’s attempts to gain access to information about potential targets.
Prevent Internet Protocol (IP) Spoofing
Internet protocol (IP) addresses provide attackers with some of the most direct methods to hijack any computer network. By impersonating other computers on the network, attackers gain access to the local area network.
A DMZ prevents IP spoofing attempts by verification. A DMZ also deploys network segmentation to grant external users least privilege access to system resources and applications.
What Runs in a DMZ?
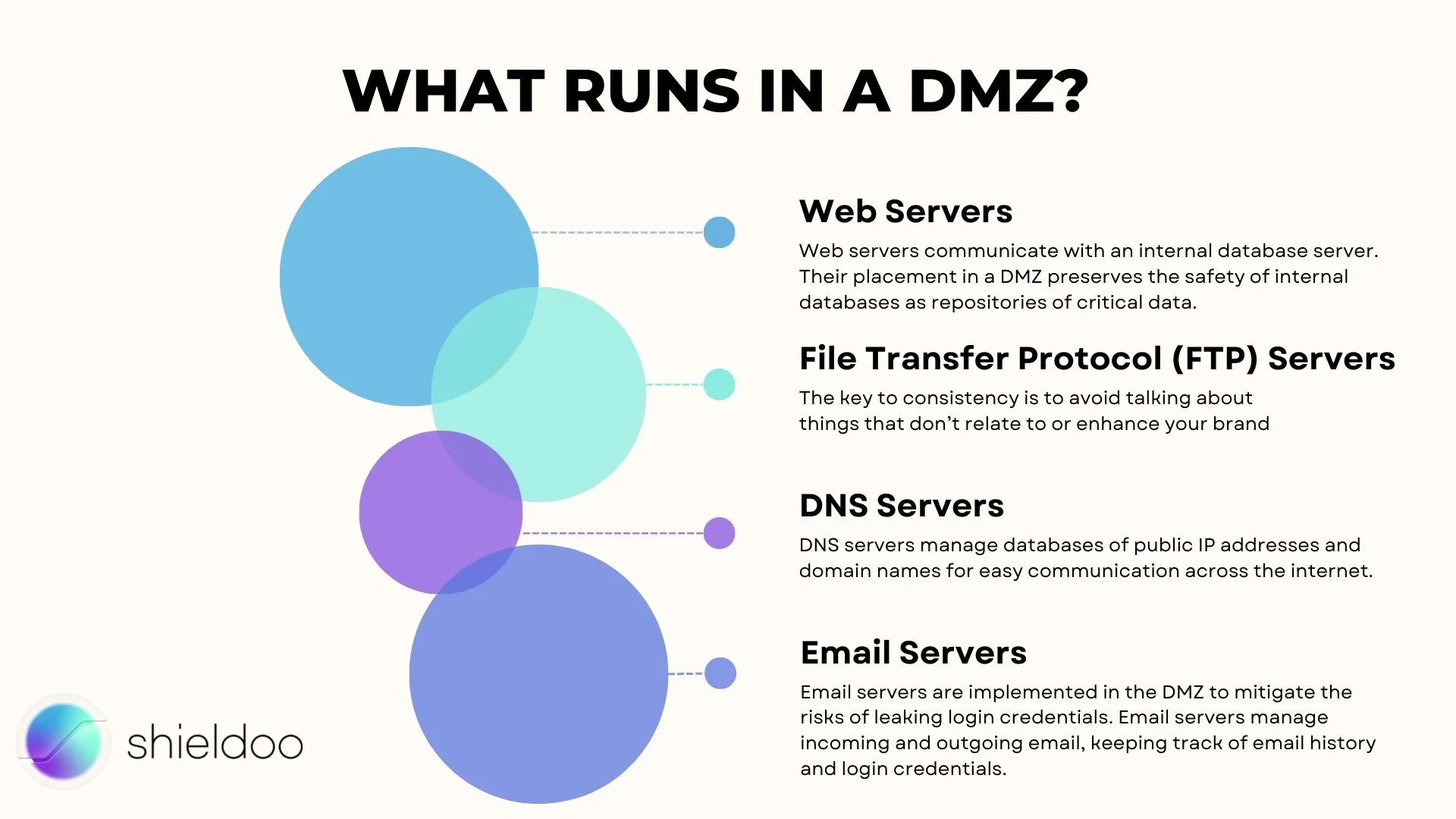
Services communicating with external networks are isolated from the internal private network and deployed in the demilitarized zone or DMZ. The common uses of DMZ that external users usually access are the following:
Web Servers
Web servers communicate with an internal database server. Their placement in a DMZ preserves the safety of internal databases as repositories of critical data. Webservers engage in direct communication with the internal database server or through an application firewall.
File Transfer Protocol (FTP) Servers
File transfer protocol, or FTP, is a network protocol that enables data transfer between computers connected on a computer network. FTP servers can manage and host content within an organization's private network. Their purpose plays acritical role in engaging with network files and resources directly. Thus, it is crucial to isolate FTP servers from internal systems to mitigate data loss or exploitation.
DNS Servers
DNS servers manage databases of public IP addresses and domain names for easy communication across the internet. Whilst DNS servers only organize public IP addresses, attacker scan manipulate these servers and execute unauthorized DNS requests that may compromise the local area network.
In a DMZ, DNS requests are limited to granting access to resources and applications shared for public use.
Email Servers
Email servers are implemented in the DMZ to mitigate the risks of leaking login credentials. Email servers manage incoming and outgoing email, keeping track of email history and login credentials, which are vulnerable to phishing attacks from suspicious internet users.
A DMZ prevents email servers from exposing themselves to risky web pages.
Applications of DMZ
DMZ is in widespread use to maintain network security in the following cases:
Cloud Services
Implementing a DMZ in cloud computing is a strategy fitting for network operating services and applications within the local area network and on the cloud for remote access. In this scenario, a DMZ records and regulates traffic moving between on-site servers and virtual networks.
Home Networks
A private home network comprised of a local area network and broadband router is also an excellent instance to implement a DMZ. The router, or an appointed device, will be configured with a DMZ host feature. This device operates outside the firewall, comparable to another DMZ. This device will not experience intermittent connections, as the rest of the devices in the home network are accessing the internet from within the firewall.
Industrial Control Systems (ICS)
Operational technology equipment is typically not built with a security infrastructure to withstand cyberattacks. That being said, a DMZ is a viable security solution.
With network segmentation, access to the internal systems of operational technology equipment is divided across the network, limiting users to least privilege access. Due to granular traffic, cybercriminals will find it difficult to invade and navigate their way through the network.
What Makes a DMZ Important?
The advent of firewalls led DMZ networks to uphold network security for organizations far and wide. DMZ networks isolate internal networks from the prying eyes of the public Internet and address pressing security vulnerabilities.
DMZs are excellent buzzer zones to run external-facing servers. These services have the most contact to untrusted networks by isolating them from the internal networks. Security threats are under complete control and mitigated by the DMZ.
Try Shieldoo™️
Cyber security is becoming more and more important, which is why we provide you with essential information in a wide variety of articles on our blog. We also developed a new tool Shieldoo™️ based on Nebula from Slack which can help you to provide secure connection between end-users and servers. You can try your own private network here.
FAQs
What is the difference between DMZ and firewall?
A demilitarised zone, or DMZ network, is a perimeter network that restricts access to the local are a network. It is a buffer area between the public Internet and the LAN. Meanwhile, a firewall is a security infrastructure that regulates traffic between networks. For instance, a DMZ is usually located between two firewalls that control incoming and outgoing traffic between the external network, the DMZ, and the LAN.
What makes up the external network?
The external network refers to any untrusted network outside the perimeter of the LAN. It usually refers to the public Internet.
Are dual firewalls more secure?
A dual firewall design for DMZ is cited to be more secure as traffic is controlled and filtered at both ends: at the front end, where traffic from external sources flows into the DMZ, and at the back end, where traffic from the internal network to the DMZ flows. Dual firewalls mitigate the risk of encountering the same security vulnerabilities.
What makes up the internal network?
The external network refers to any untrusted network outside the perimeter of the LAN. It usually refers to the public Internet.





