Estimated read time: 8 minutes
The Internet is looming with various security threats for individuals and companies. To protect sensitive information from the public eye, IT departments would set up firewalls and construct private networks. A virtual private network (VPN) became necessary for employees to access applications or resources stored in the business network.
Over time, how companies accomplish work and engage in business transactions over the Internet evolved. Cloud-based services are enabling organizations of all sizes to scale operations faster and more efficiently. However, a traditional VPN can do more harm than good in handling user traffic and network access privileges.
Peer-to-peer connections construct and maintain a reliable infrastructure to seamlessly connect computers across the globe. Nebula revolutionizes how computers can communicate and keep said communications safe and secure from snooping entities on the vast space of the Internet.
What Is Nebula?
Nebula is a mesh network with a peer-to-peer connection, allowing machines to communicate and transfer data with one another. A central node, or lighthouse, directs the communication path between machines, or nodes, within a network. Lighthouses work efficiently, reducing waiting time.
Slack engineers Nate Brown and Ryan Huber brought forth Nebula to address the pressing need for encrypted connectivity. As networks grow, traffic is expected to increase. However, most enterprise solutions lack the scalability and interoperability for business networks to fully expand and monitor traffic quality.
Nebula is built on the Noise Protocol Framework, encrypting end-to-end connections and supporting user identity authentication checkpoints and certificates. Machines in a mesh network communicate directly, allowing for low latency and fast data exchange.
Setting Up a Nebula Network

Nebula is an open-source software-defined network. Any individual machine, computer network, or data center can establish a Nebula mesh without adhering to strict IP address segmentations.
To set up a Nebula network, you will begin with creating a certificate authority, which will provide the keys for every computer that will be part of the mesh network. Every connected computer will be required to download the Nebula binary or distribution package, generate a security certificate, and set configuration files. These files will be distributed within the network to enable each computer to run Nebula.
Below is a quick start guide to Nebula:
1. Download the necessary Nebula binaries for your machine’s operating system and platform. These binaries and other packages are available to download for free from the official Nebula repository on GitHub.
2. Establish a discovery node, or the lighthouse of the Nebula network. Lighthouses enable nodes in the network to find and communicate with each other, regardless of geographical location. The lighthouse node is the sole static IP address in the mesh network.
Lighthouse nodes are compatible to run on cloud-based hosting services. The creators of Nebula suggest DigitalOcean as a budget-friendly hosting option for your lighthouse node necessities.
3. Establish a Nebula certificate authority. This plays a key role as the root of trust for your Nebula network. Below is an example of creating a certificate authority:
root@lighthouse:/opt/nebula# ./nebula-cert ca -name "MyNewNebulaMeshNetwork"
This will create ca.key and ca.cert files in your working directory. The ca.key file is used to authorize and sign certificates for individual nodes. It is also the most sensitive file in the directory. It is not necessary for running the Nebula mesh itself; thus, it is highly recommended to secure this file in an encrypted place outside the current directory.
4. The certificate authority will then generate host keys and certificates. Identify IP addresses for every node and the network range of the mesh.
5. Set up configuration files for every node. Verify that am_lighthouse:true is set on the lighthouse node. As for the individual nodes, check whether the lighthouse node is defined and is listed among the lighthouse hosts section.
6. Copy nebula credentials, configuration files, and binaries for every host. However, omit copying the ca.key file to the individual nodes.
7. Your nebula mesh network is all set. Run Nebula on each host with the following prompt:
./nebula -config /path/to/config.yml
What Is Connectivity Like in a Nebula Mesh Network?
A Nebula network enables computers to communicate across IP ranges without compromising on speed and security. Every Nebula mesh has an assigned lighthouse node that allows computers in the network to seek out the quickest and most direct routes from one endpoint to another in exchanging data.
Nebula Security: How Safe Is a Nebula Mesh?
The founders of Nebula sought to address the flaws and vulnerabilities of existing third-party networking and security solutions. Conventional VPNs are challenging to optimize according to present-day encryption protocols because of limited scalability. In addition, user-defined groups established by cloud-based service providers are not interoperable across different hosting services, complicating traffic filtering as networks expand.
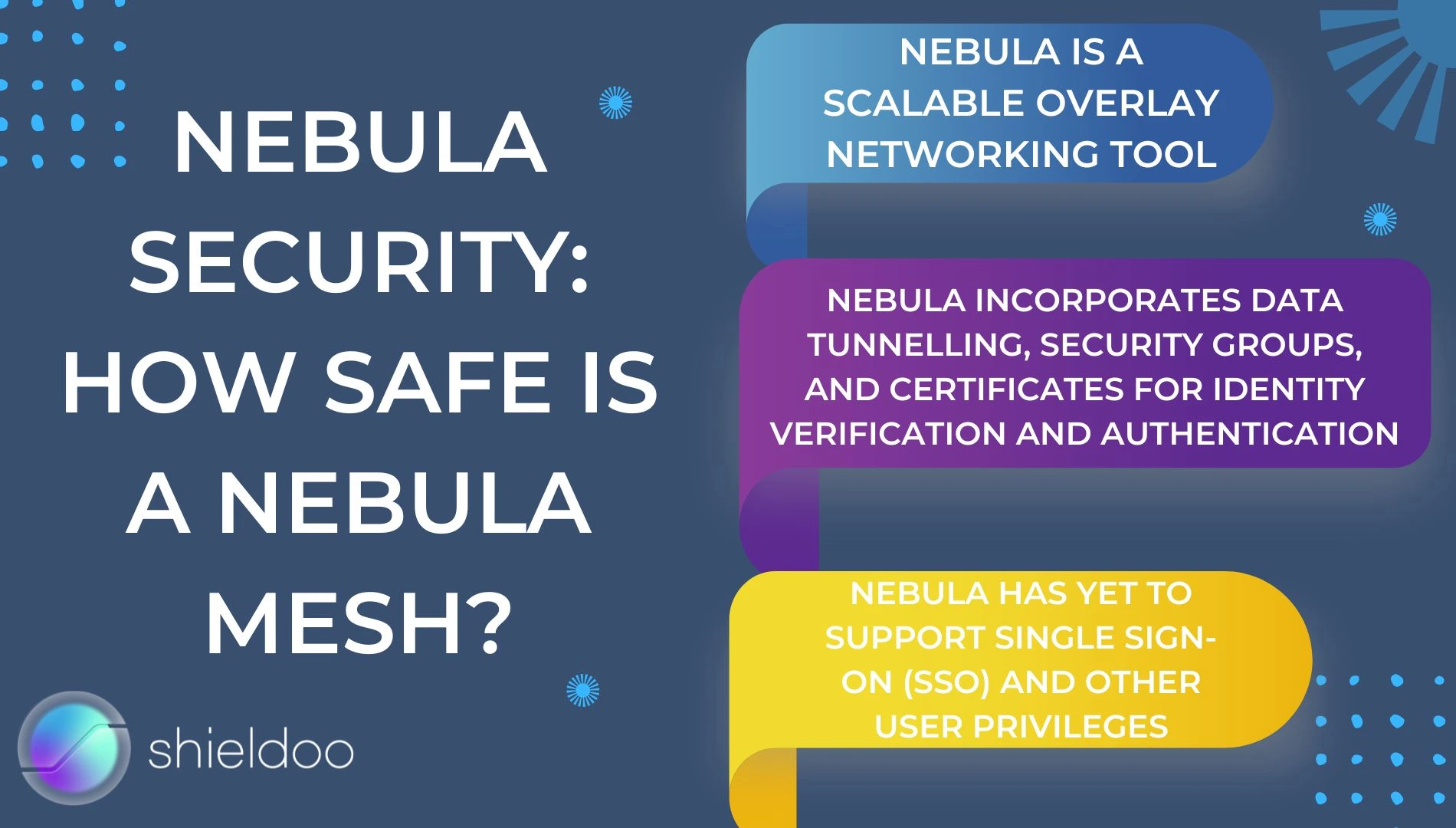
Nebula is a scalable overlay networking tool, which aims to address all security vulnerabilities while simplifying network management for individual users, computer systems, and data centers. It uses the Elliptic curve Diffie-Hellman (ECDH) for key exchange. Mutual authentication between machines is made possible by AES-256-GCM.
On top of encryption controls, Nebula incorporates data tunnelling, security groups, and certificates for identity verification and authentication. These solutions enable Nebula to offer well-rounded network management and security.
However, user access controls are limited. Nebula has yet to support single sign-on (SSO) and other user privileges. Users may find this an inconvenience, as they have to resort to a separate software solution to manage user credentials.
Shieldoo™️: A Sleek and Intuitive Alternative to Nebula Mesh

Nebula is an open-source overlay networking tool that lets users define their lighthouses and networks as they wish. However, setting up one can be challenging for users with little to no experience in coding.
Fortunately, the rise of closed-source overlay networks has simplified the process for many business users and organizations. Shieldoo™️ is an excellent alternative for any business to set up a global overlay network without the nitty-gritty of manually managing distribution packages, keys, and user certificates.
Shieldoo™️ is a next-generation secure network that lets business networks secure communications and user activity from anywhere in the world. It works similarly to a Nebula network, with additional support for SSO, multi-factor authentication (MFA), and zero trust.
Experience Plug-and-Play Integration and a Fortified Security Infrastructure with Shieldoo™️

Nebula is an excellent overlay networking tool for system administrators that prefer to work with the nitty-gritty details of security certificates and host control. For business networks and casual consumers, however, convenience and efficiency are more significant. Shieldoo™️ introduces convenient overlay networking wherever, whenever with zero trust technology and plug-and-play integration. Users can enjoy 100% uptime of security protocols to ensure all online activity is encrypted and protected from the lurking threats of the public internet.
Try out Shieldoo™️ and experience hassle-free encryption and security reinforcement for your business network.
FAQs
What is Nebula?
Nebula is an overlay networking tool designed by engineers at Slack to allow business networks to establish secure, end-to-end communications across the globe. Today, Nebula is owned by Defined Networking.
Is Nebula a VPN?
Yes. However, unlike the conventional VPN, Nebula is a distributed VPN mesh. Individual nodes communicate directly through tunnels rather than relying on a central hub to manage connections.
Is Nebula available for free?
Yes! Nebula is an open-source project. Nebula binaries and distribution packages are available for download on GitHub.





