Estimated read time: 8 minutes
What Is a Business VPN?
A virtual private network, or VPN, is an encrypted connection for users to connect and access private data across a public network. VPNs provide a cloak of privacy, keeping away prying eyes and ears.
For businesses, securing a private connection between employees and company servers is a top priority. By adding a VPN to their security architecture, critical assets and other resources are protected from suspicious activity.
How Do Business VPNs Differ From Consumer VPNs?
Most Internet users have experienced using a VPN to access certain geo-locked websites. This is a typical use of consumer VPN. However, businesses utilize VPN to add a security and privacy layer to their private network.
A business VPN is specially developed to cater to the needs of multiple users. As employees access files on the server at recurring times of the day, data loss and internal breaches are highly plausible vulnerabilities. A business VPN mitigates such risks by requiring authorized access.
A consumer VPN replaces a user’s IP address whenever they enable the VPN or switch servers. Meanwhile, a business VPN is a higher-level VPN service providing exclusive use of a static IP address.
What Good Is a Business VPN?
Increased engagement in work matters on the Internet means more employees are operating from a remote setup. This means proprietary data from the business network has to be accessed through devices connected to a public network. An employee can be unknowingly tracked by attackers and leak critical assets.
A business VPN reinforces the security of remote access by encrypting user traffic. This allows the company to keep a close watch on user activity, all the while cloaking transactions between employees and the company’s servers from the public.
Different Kinds of Business VPNs
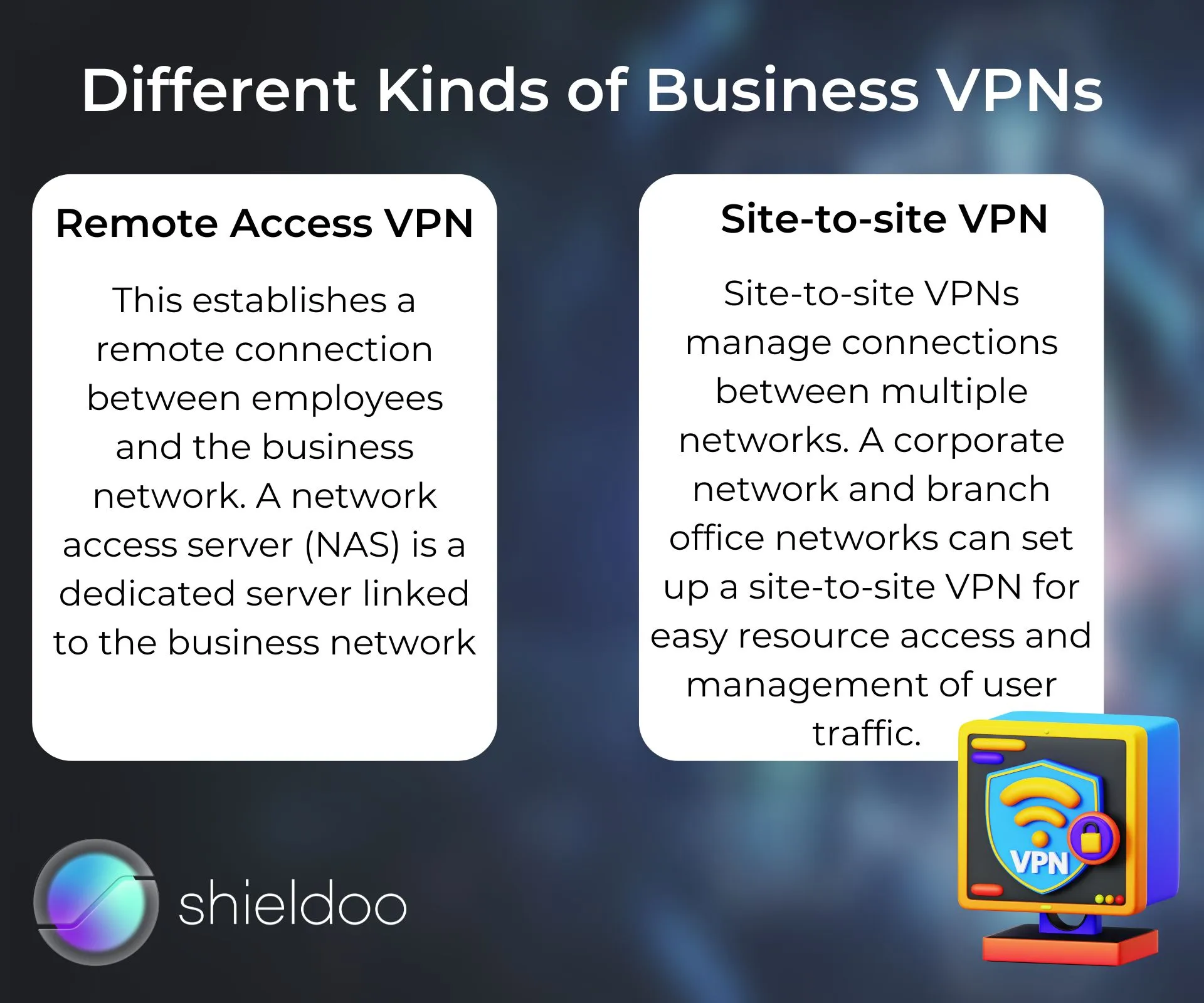
It is a common misconception that business VPNs all operate the same way. To find out which business VPN fits your security needs and preferences, let’s discuss the two kinds of business VPNs below.
Remote Access VPN
This establishes a remote connection between employees and the business network. A network access server (NAS) is a dedicated server linked to the business network. To connect to the NAS and retrieve data from the network, an employee enables a VPN client. This software creates an encrypted tunnel, providing secure access to the NAS and preventing user traffic from being ambushed by unauthorized parties.
Site-to-site VPN
Site-to-site VPNs manage connections between multiple networks. A corporate network and branch office networks can set up a site-to-site VPN for easy resource access and management of user traffic.
Advantages of Integrating a Business VPN
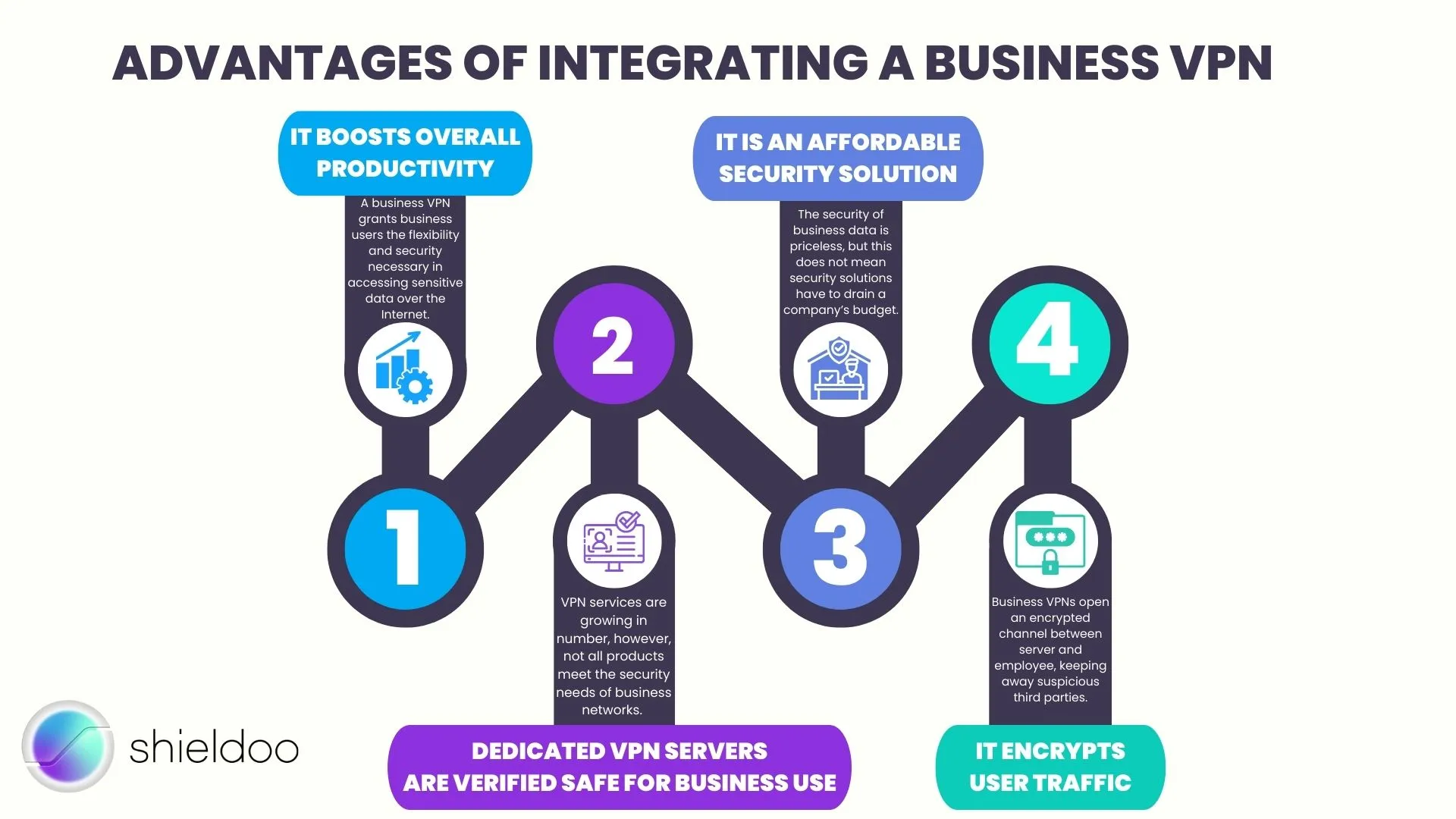
A business VPN grants business users the flexibility and security necessary in accessing sensitive data over the Internet. On top of reinforcing privacy measures, here are other advantages that make a business VPN an essential security solution.
It boosts overall productivity.
Gone are the days of employees traveling back and forth to the office to connect and access business data. With a business VPN, employees have secure remote access to resources wherever they are. As more and more public Wi-Fi points are becoming accessible outside the office, employees can get more work done, without running the risk of exposing sensitive data to the public network.
Dedicated VPN servers are verified safe for business use.
VPN services are growing in number, however, not all products meet the security needs of business networks. A dedicated business VPN is designed to provide wide-scale use for the employees, with all devices linking only to one IP address and VPN server. Thus, the server is only accessible to business users with authorized access. Bigger organizations can have more VPN servers and, therefore, more public IP addresses.
It encrypts user traffic.
Data leaks and cyberattacks begin by tracking down the source of traffic volume. Business networks can prevent such threats by rendering user activity invisible to the public eye with a business VPN. Business VPNs open an encrypted channel between server and employee, keeping away suspicious third parties from gaining access to the company network.
It is an affordable security solution.
The security of business data is priceless, but this does not mean security solutions have to drain a company’s budget. Business VPNs are affordable upgrades to your security architecture. By easing the troubles of the IT department in keeping security risks at bay, a business VPN effectively transforms the security measures and levels your company observes.
Disadvantages of Using a Business VPN
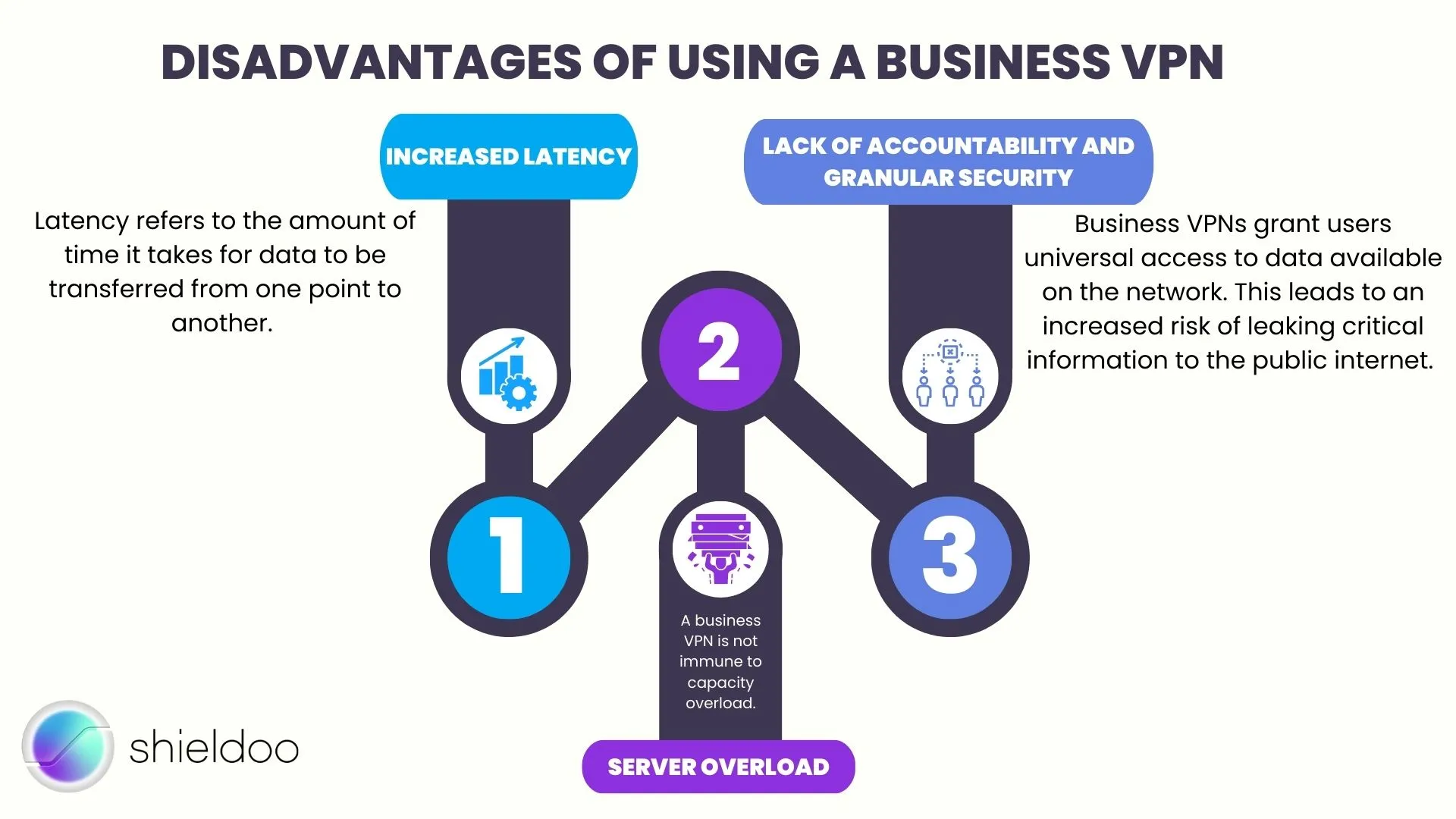
While business VPNs made remote work more secure and viable for many enterprises, they do come with downsides. The gravity of a business VPN’s disadvantages may vary depending on the service provider, IT literacy of business users and more.
Increased Latency
Latency refers to the amount of time it takes for data to be transferred from one point to another. In the case of a business VPN, data travels across a longer route, as the VPN service provider will route data to the VPN server before it reaches its destination. Users may experience a delay in loading images, videos, websites and more through a business VPN.
Server Overload
A business VPN is not immune to capacity overload. A VPN server may experience handling a number of data requests well over its capacity, which can lead to slower responses and dropped requests. An overloaded VPN server also affects latency, which can impair the productivity of business users. Most enterprises would consider managing an extra VPN server, but this can be a costly and rather impractical resolution.
Lack of Accountability and Granular Security
Business VPNs grant users universal access to data available on the network. This leads to an increased risk of leaking critical information to the public internet.
In addition, business VPNs don’t keep track of activities on the network to uphold user privacy. This leaves the IT security team with the problem of needing help to diagnose or troubleshoot issues.
How Shieldoo™️ Can Protect Your Company Data
Shieldoo™️ is a provider of secure network (mesh) technology, reinforcing VPN service with cloud security infrastructure for scalable operations and unmatched network security, wherever you are in the world.
Unlike traditional VPNs, the beauty of Shieldoo™️ comes with layer after layer of security and ease of operating a security solution for large-scale use. Secure your company networks with the swift integration of Shieldoo™️ in your security architecture. In just a few minutes, your employees can enjoy secure remote access to critical company data.
Our security technology is flexible. We can initiate security solutions on the cloud, strictly for legacy systems or a hybrid of cloud and hardware operations to maximize the security and privacy of company resources.
Shieldoo™️ is compatible with most operating systems, providing full security and privacy to business users, no matter the device they choose to work on. Windows, macOS, Linux, iOS and Android devices are all supported by Shieldoo™️.
What Can Shieldoo™️ Offer?
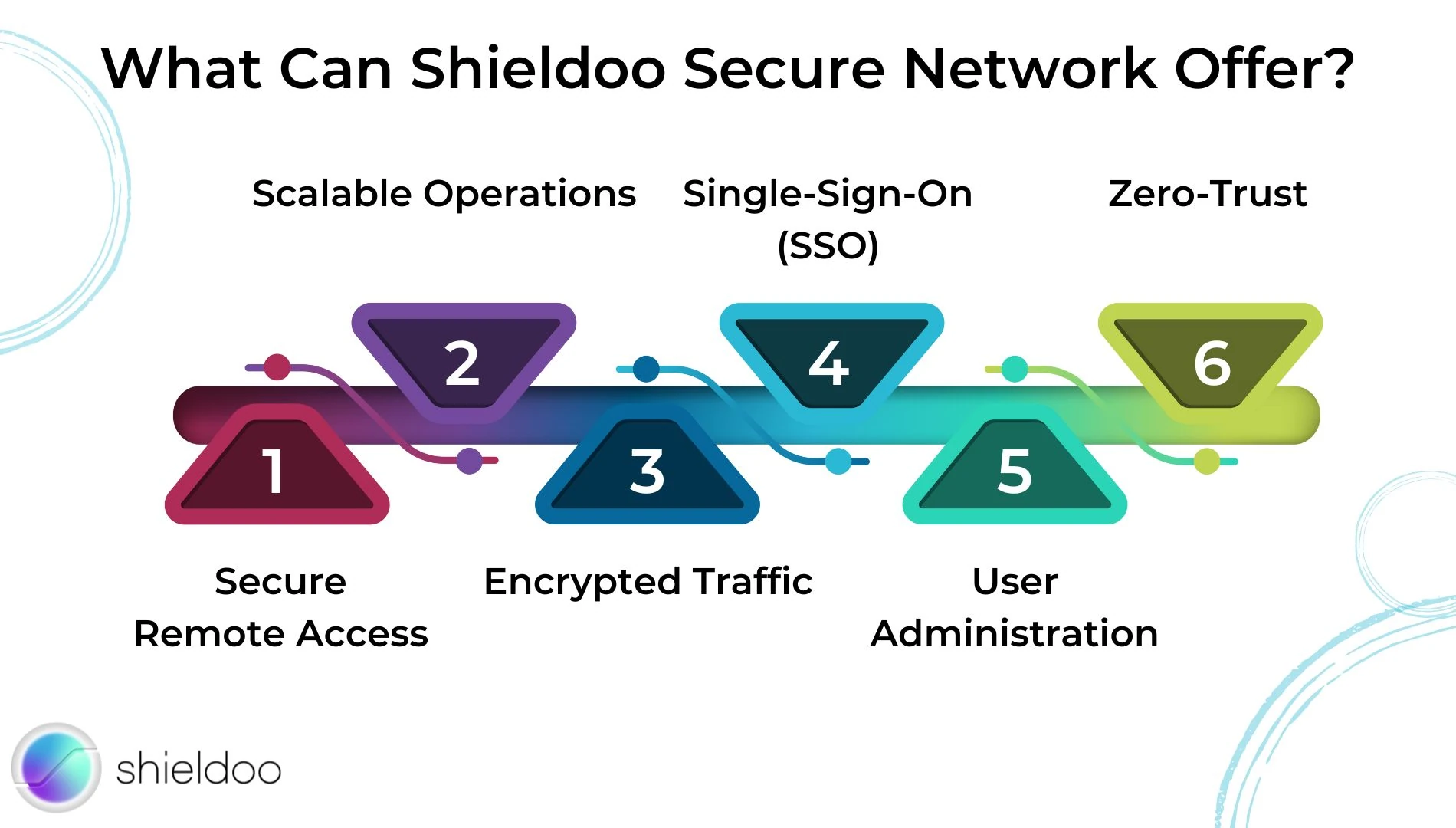
Secure Remote Access
Connect to the company network from anywhere in the world, without risking the privacy of company resources. Our security services deploy reliable remote access and eliminate security risks upon activation.
Scalable Operations
Our security services are customized to meet everybody’s needs. No matter how big or small your business is, we can provide a sustainable solution to elevate your security measures and enhance employee productivity.
Encrypted Traffic
Advanced Encryption Standard (AES) 256-bit encryption disables attackers from snooping into critical data. Shieldoo uses Elliptic-curve Diffie-Hellman key exchange(ECDH).
Single-Sign-On (SSO)
Hassle-free login with a single set of credentials. Shieldoo™️ supports SSO with platforms such as G Suite and Azure AD.
User Administration
Onboard team members and manage access permissions from a universal control panel. We enable centralized billing for reduced risk and easier management of payment details.
Zero-Trust
Shieldoo™️ operates security solutions reinforced by zero trust technology. On top of securing endpoints and user traffic, Shieldoo™️ verifies and authenticates privileged access of business users. We deploy two-factor authentication (2FA), software defined perimeter (SDP), and zero trust network access (ZTNA).
How Does Your Business Benefit From Shieldoo™️?

Shieldoo™️ engages in a holistic and sustainable approach to securing your network. We believe that with a security network (mesh), your business will experience changes from security and privacy, operations, all the way to the C-suite.
Security Level
At a security level, Shieldoo™️ mitigates the risk of data loss and cyberattacks, while enhancing user authentication and verification. Changes in the network, such as access requests and file changes, are tracked in real time through auditing.
Operational Level
Security infrastructure progresses according to the user base and needs of your network. There’s no limit to the number of devices we support as we tailor our solutions to your business and security goals.
C-Level
Our flexible and reliable solutions empower remote workers to accomplish tasks at a comfortable pace and environment, improving productivity and overall performance.
Try Shieldoo™️
Cyber security is becoming more and more important, which is why we provide you with essential information in a wide variety of articles on our blog. We also developed a new tool Shieldoo™️ based on Nebula from Slack which can help you to provide secure connection between end-users and servers. You can try your own private network here.
FAQs
What is a virtual private network?
A virtual private network, or VPN in short, is a security solution that protects connections to a private network from the public eye.
What are the advantages of using a business VPN?
A business VPN is an affordable security service. With its basic implementation, users can protect their activity online from prying eyes. A business VPN also enables employees to work from a remote location.
What are the disadvantages of using a business VPN?
A business VPN often slows down connection speeds, hampering the productivity of users. A medium-sized enterprise may also require more than one VPN server to accommodate multiple requests at a time. In addition, business VPNs do not guarantee the security of critical data stored on the network. All users have access to every resource available, raising the risk of internal data breaches and cyberattacks.
How does the number of servers affect VPN services?
The number of servers can determine the capacity of a VPN service. If a VPN service has multiple servers, they can accommodate more users at a time. Business VPNs use a dedicated VPN server to safeguard activity and prevent the entry of unauthorized individuals.
Do small businesses require a VPN?
Small businesses operating remotely require a VPN to protect business affairs and data from malicious individuals on the public internet.





