Estimated read time: 7 minutes
What Is RDP?
RDP is short for Remote Desktop Protocol, a network access protocol that enables users to connect to a host server remotely. With RDP, users can access files, applications and other resources from the host server on a client device from a remote location.
How Does Remote Desktop Protocol (RDP) Work?

To understand how RDP works, setting a real-world example would be the best.
Business users often use an office computer when working, with a separate personal computer, such as a laptop, at home. Should they need to work on a task at home, business users can gain access to office files with RDP and perform tasks such as printing copies of documents without leaving for the office.
RDP shares information onscreen from the host server to the client, while receiving peripheral device input from the client device to the server. RDP grants remote users access to resources and command prompts stored in a host server. Multiple channels are at work to deliver the content requested by clients. It features a graphical interface where business users can get a virtual desktop view of their office computer, all while interacting with a mouse and keyboard at home.
Microsoft developed Remote Desktop Protocol (RDP) to support remote communication between client devices and a host server. For RDP to be employed, clients must install RDP client software, whereas host servers require RDP server software.
RDP server software is built into all Windows operating systems. Remote clients, on the other hand, have to install an RDP client software to connect to the host server. Microsoft provides its official RDP client software called Remote Desktop Connection (RDC), known as the Terminal Services Client in older iterations of the operating system.
With Remote Desktop Connection installed, a remote user gains permission to establish a connection with any host computer and access existing files from the convenience of their remote Windows PC or any device running a compatible operating system.
RDP client and server software are also available for other operating systems. In the case of Microsoft, RDP and other remote desktop services are crucial not only for remote computer access but also as a virtual computing solution. Cloud computing services rely on RDP for scalable work management and collaboration.
What Is RDP Used For?
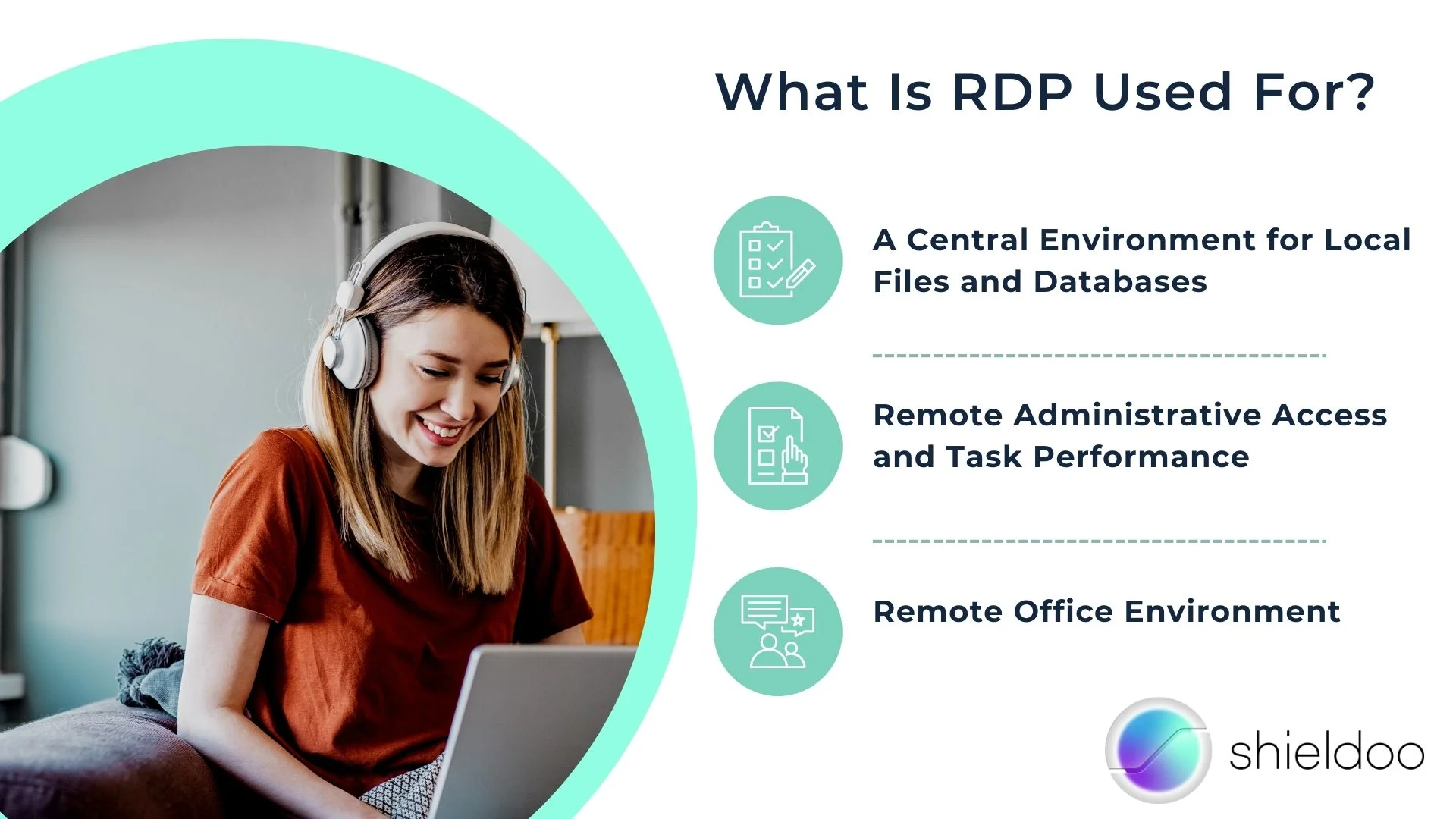
RDP offers plenty of use cases for business users who navigate their daily lives in a fast-paced technological revolution. With RDP, work can be managed outside the typical office setting, enabling employees to collaborate and accomplish tasks regardless of their location.
A Central Environment for Local Files and Databases
With a remote desktop implemented in the workplace, the long wait for processing access requests is eliminated. Tapping on the remote desktop connection gives the employee direct access to the necessary files, applications, or data.
Remote Administrative Access and Task Performance
Remote desktop services support administrative tasks such as maintenance, server updates, troubleshooting, software installation and more. Technical support is more fluid and efficient with RDP.
Remote Office Environment
RDP saves employees the trouble of traveling back and forth to the office in emergency cases. From the comfort of their home, the employee can tap into the office desktop and interact with the files or databases they need as if they were in the office.
What Are the Benefits of RDP?

The need for instant, on-the-go access to critical resources is prevalent in present society. Now that enterprises have a better understanding of ideal working environments after the COVID-19 pandemic, remote desktop access is all the more a necessity.
Increased Data Security
Remote desktop services keep the IT security team alert for fixes and maintenance checks on the office’s files and applications. In addition, remote desktop access enables tech support to run data backup and recovery immediately.
Reduced Costs and Resource Optimization
Implementing remote desktop access in the office supports the bring-your-own-device policy. This allows employees to make use of personal computers in completing tasks. Employees are welcome to install office applications on their laptops. Thus, the department has the option to reallocate resources intended for investing in new technology.
Enhanced Productivity
Empowering employees with innovative technology such as remote desktop services boosts morale and overall productivity. A remote desktop presents employees with the golden opportunity to work in an environment of their choice. Supervisors may be pleasantly surprised with their subordinates’ performance after working remotely and working on a more optimized computer.
Swift and Easy Data Management
RDP in the workplace offers business users immediate access to files stored locally on the office desktop. Instead of personally fetching files or running updates from the office, users can tap on the remote desktop connection from their personal devices.
Security Vulnerabilities of RDP
Despite its flexibility, RDP comes with several vulnerabilities. As cyberattacks become more complex for the IT department to detect and eliminate, it is worth taking note of the issues that come with adopting RDP in the workplace.
BlueKeep
BlueKeep is a vulnerability that brought trouble for Microsoft’s default RDP server. It affected devices running Windows 2000, Windows 7 and Windows Server 2008 R2. BlueKeep allowed remote code execution and attackers could exploit this and disrupt systems. On May 2019, BlueKeep was addressed with a patch update. However, this patch does not guarantee that BlueKeep is no longer affecting devices. Research shows that over 240 thousand devices are still at risk of being exploited, suggesting the possibility that bugs other than BlueKeep have yet to be addressed.
Open Ports
RDP uses several open ports to allow clients to connect with the host. These ports are prone to cyberattacks, as access generally consists of weak passwords. As remote work becomes the new norm, enterprises and the IT sector expect cyberattacks to become prevalent.
Bring Your Own Device (BYOD) Policy
This policy allows business users to depend on personal devices to perform tasks. While this saves the office from costly investments in new technology, it can also bring about security and compliance risks.
Employees may use third-party applications to speed up their work process, without approval from the IT department. The introduction of shadow IT to the workplace endangers critical client data and risks business governance. Additionally, client devices do not share the same security solutions as those with office computers. Checking device health is crucial to mitigate data breaches.
BYOD reduces operational costs and empowers business users – however, it also comes with vulnerabilities that are difficult to overlook. For a more reliable and secure RDP, enterprises may want to consider complementing RDP with a virtual desktop infrastructure (VDI).
What Should Be Considered as the Baseline for an RDP Security Policy?

Increasing the network’s security for safe and streamlined RDP use is possible. When drafting an RDP security policy, consider integrating the following:
1. Account Lockout
Remote desktop services implement an account lockout to safeguard the system from cyberattacks. It is similar to logging in and inputting incorrect credentials several times. With account lockout, the client device can lock the account for a period of time after making incorrect password guesses.
2. Two-Factor Authentication
With two-factor authentication, a user will be notified of a login attempt on another mobile device, such as their mobile phone. Upon recognizing it is an unknown login attempt, they can immediately report a suspected cyberattack to IT or tech support.
3. Least Privilege Access
RDP lacks the nature of role assignment for remote users accessing the RDP server. Implement least privilege access to limit the accessibility of critical information and databases. With least privilege, clients have minimal access to the remote server. Hence, they can only access one file at a time.
4. Firewall Listening Ports
Run RDP with firewall listening ports. This hides the Remote Desktop from hackers lurking around the network for an open remote desktop connection.
5. Encryption Tools
Ensure the confidentiality of data accessible on your devices with encryption technology. This prevents sensitive data from leaking.
6. Privileged Account Manager (PAM)
In line with implementing least privilege access, a privileged account manager (PAM) secures access to RDP through several access management methods. These include:
- Remote Desktop Protocol Relay (RDP relay)
- Direct Remote Desktop Protocol (Direct RDP)
- Run as Privileged User
- Credential Provider (CP)
- Application SSO
7. Software Updates
Double-check the version of the RDP client and server software you are running. Update to the latest versions to ensure vulnerability fixes are reflected on your system.
Replace RDP With Shieldoo™️, the Next-Gen Secure Mesh
Remote access technology is all the rave, but not all solutions are made equal. Shieldoo™️ is a zero trust network access (ZTNA) solution that runs granular access-control lists (ACLs) for limited access to resources as specified by user request.
With Shieldoo™️ secure network, remote access is entirely on the cloud and is not tied to virtual private networks (VPNs) for easier scaling of remote access support. Business users can be deployed far and wide, yet they retain access to the business network.
In addition, Shieldoo™️ eliminates the need for a physical resource directory. It establishes a peer-to-peer (P2P) connection between the devices communicating in the network, redirecting data traffic to where it is requested immediately.
FAQs
What Is RDP?
RDP is short for Remote Desktop Protocol, a network access protocol that enables users to connect to a host server remotely. With RDP, users can access files, applications and other resources from the host server on a client device from a remote location.
Is RDP a VPN?
A remote desktop protocol and a virtual private network adopt different methodologies in granting remote user access. An RDP establishes remote communications between RDP clients and an RDP server. A VPN is a security solution that limits network access from the local network.
What is the best remote desktop software?
The official RDP software from Microsoft is among the well-known solutions on the market. Other kinds of remote desktop software are available for non-Windows operating systems as well. Viable RDP software alternatives include Remmina (Linux), NoMachine (macOS, Linux, and Windows), and X2Go (Linux, macOS, and Windows).
What is needed to run Remote Desktop Connection?
On Windows PCs, go to the taskbar and click on the search box. Type in Remote Desktop Connection and select the application. Input the PC name you wish to connect to and click Connect. For mobile Windows, iOS and Android devices, download and install the Remote Desktop application. Input the name of the PC you wish to connect to and select it. Wait for a successful connection between the devices.
Is Remote Desktop Protocol secure?
RDP alone is not a secure communications solution. Integrate it with advanced security solutions like zero trust network access, multi-factor authentication and single sign-on for a more secure remote workstation.





